Bluesky Grapples with Prolonged Cyberattack: Decentralized Social Network Faces Service Interruptions Amidst Sophisticated DDoS Onslaught
Bluesky, the emerging decentralized social network, continued to experience significant service disruptions on Friday, extending an outage that began earlier in the week. Chief Operating Officer Rose Wang explicitly attributed the ongoing issues to a sophisticated Distributed Denial-of-Service (DDoS) cyberattack. The platform’s website and application have been intermittently struggling, presenting users with a frustrating mix of slow loading times, error messages, and complete unavailability of certain features. This prolonged incident marks a critical test for the relatively new social media contender, challenging its infrastructure and user trust as it strives to establish itself in a competitive landscape dominated by established giants and a growing array of decentralized alternatives.
Unpacking the Attack: Understanding DDoS and Its Impact
On Thursday evening, Bluesky officially confirmed that a "sophisticated Distributed Denial-of-Service (DDoS) attack" was the root cause of the widespread service issues. The attack originally commenced on April 15, at approximately 8:40 p.m. ET, and has persisted, making for a challenging week for the platform’s engineering team and its user base.

A DDoS attack is a malicious attempt to disrupt the normal traffic of a targeted server, service, or network by overwhelming the target or its surrounding infrastructure with a flood of internet traffic. Unlike a traditional denial-of-service (DoS) attack, which typically uses a single computer and internet connection to flood a target, a DDoS attack employs multiple compromised computer systems as sources of attack traffic. These "botnets" can consist of thousands or even millions of devices, including computers, IoT devices, and other network-connected machines, all remotely controlled by an attacker.
The sheer volume of junk web traffic generated by a DDoS attack is designed to overload the target’s servers, exhausting their capacity to process legitimate requests. This effectively knocks the service offline, preventing legitimate users from accessing the website or application. While DDoS attacks generally do not involve intrusions into a company’s internal systems or unauthorized access to private data, their impact can be profoundly disruptive. For a social media platform like Bluesky, which relies heavily on real-time user interaction and constant availability, such an attack can severely degrade user experience, halt new user sign-ups, and erode confidence in the platform’s reliability and security posture.
The motivations behind DDoS attacks are varied. They can range from ideological hacktivism and competitive sabotage to simple acts of vandalism or even extortion. The cost of such attacks to businesses can be substantial, encompassing not only direct financial losses from lost revenue and mitigation expenses but also intangible damages such as reputational harm, decreased user loyalty, and potential legal liabilities for service level agreement breaches. According to a recent report by Statista, the average cost of a DDoS attack for enterprises can range from tens of thousands to millions of dollars, depending on the duration and severity, underscoring the serious nature of the threat Bluesky is currently facing.

A Chronology of Disruptions and Bluesky’s Response
The timeline of the incident illustrates a developing crisis for Bluesky:
- April 15, 8:40 p.m. ET: The initial service interruptions began, though the cause was not immediately identified publicly.
- Wednesday, April 17, 3:46 a.m. ET: Bluesky protocol engineer Bryan Newbold publicly acknowledged the difficulties, posting, "oof, our services are getting hit pretty hard tonight." This indicated that the Bluesky team was aware of and actively responding to an escalating issue.
- Thursday Evening: Bluesky officially confirmed the nature of the problem, identifying it as a "sophisticated Distributed Denial-of-Service (DDoS) attack." This confirmation came via a post on the official Bluesky account, detailing that the attack was "impacting our operations, with users experiencing intermittent interruptions in service for their feeds, notifications, threads, and search."
- Ongoing Friday: The disruptions continued into Friday, with users across various time zones reporting difficulties accessing the platform. Bluesky COO Rose Wang further reinforced the attribution to an ongoing cyberattack.
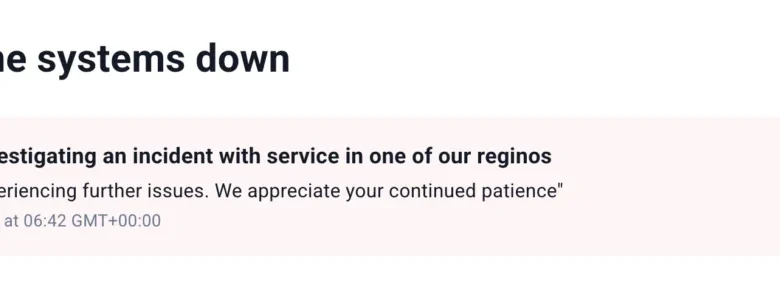
- Lack of Immediate Resolution: When initially approached for comment on Thursday, Bluesky directed inquiries to its status page (status.bsky.app) and its dedicated status account (@status.bsky.app) for updates. However, the status page itself became intermittently unavailable, further complicating communication and user access to critical information.
- Data Integrity Assured: Crucially, Bluesky stated that despite the extensive disruptions, it had found no evidence of unauthorized access to private user data, a common concern during any cyberattack. This assurance is vital for maintaining user trust, even as service remains compromised.
- Scheduled Update: Bluesky announced that it would provide another update on the status of the attack and its mitigation efforts by 1 p.m. ET on Friday, signaling an active, albeit challenging, battle against the attackers.
Throughout this period, the user experience on Bluesky has been significantly degraded. Intermittent outages mean the site and app might load slowly at times, only to display error messages moments later. Examples of user-facing issues include messages like, "This feed is currently receiving high traffic and is temporarily unavailable. Please try again later. Message from server: Rate Limit Exceeded," particularly affecting popular feeds such as "Discover" or the official "Bluesky Team’s" feed. Visiting individual user profiles has also frequently resulted in error messages, forcing users to refresh repeatedly or abandon their attempts. The presence of a typo ("reginos" instead of "regions") on an early status page message further hinted at the high-stress environment the Bluesky team was operating under as they grappled with the attack.
The Decentralized Advantage (or Challenge): AT Protocol and Other Instances
A significant aspect of Bluesky’s architecture, and one that offers both unique challenges and potential resilience, is its foundation on the open-source AT Protocol (Authenticated Transfer Protocol). Unlike traditional centralized social networks where all data and services are hosted on a single company’s infrastructure, the AT Protocol is designed to be decentralized. Bluesky itself operates as one of the primary "Personal Data Servers" (PDS) or instances within this larger federated network.

Notably, while Bluesky’s primary instance has been under siege, other communities that run their own infrastructure on the underlying AT Protocol have largely remained functional. An exemplary case is Blacksky, a separate community operating on the AT Protocol. Blacksky’s team confirmed to TechCrunch that they experienced a "significant spike" in migration requests from Bluesky users over the past 12 hours. This influx was not only from individual users seeking stable access but also from developers and other ATmosphere founders, such as Sebastian from Eurosky, who actively promoted Blacksky’s services as an alternative during Bluesky’s downtime.
This situation vividly illustrates both the promise and the current limitations of decentralization in practice. The fact that other instances built on the AT Protocol can continue to operate independently when the main Bluesky instance is attacked highlights a core benefit: no single point of failure for the entire network. If one PDS goes down, others can theoretically continue, and users can migrate their data and identities to a different server. This contrasts sharply with centralized platforms like Twitter (now X) or Facebook, where a successful attack on their core infrastructure would bring down the entire global service.
However, the incident also exposes a vulnerability: if the most prominent and widely recognized instance (Bluesky) is heavily impacted, it still significantly affects the overall user experience and public perception of the entire ecosystem. Many users may not fully grasp the distinction between "Bluesky the app" and "the AT Protocol ecosystem." For them, if Bluesky is down, the entire project appears to be struggling. The challenge for Bluesky and the AT Protocol community moving forward will be to educate users on these distinctions and to ensure that the ease of migration and the resilience of other instances are clearly communicated and readily accessible during such events.

Broader Implications for Bluesky and the Fediverse
The ongoing DDoS attack carries several significant implications for Bluesky and the broader fediverse landscape.
- User Trust and Retention: For an emerging platform like Bluesky, which only recently opened its doors to the public after an extended invite-only phase, maintaining consistent uptime is paramount for building and retaining user trust. Frequent or prolonged outages can lead to user frustration, potentially driving them back to more stable, albeit centralized, alternatives or deterring new users from joining. Users, especially early adopters, often tolerate some growing pains, but security vulnerabilities and extended downtime test their loyalty.
- Competitive Landscape: Bluesky is vying for attention in a crowded social media market, competing with giants like X (formerly Twitter), Meta’s Threads, and other decentralized platforms such as Mastodon. An attack of this magnitude, while common in the tech world, can undermine its appeal as a reliable alternative. Competitors, particularly other fediverse projects, might leverage this incident to highlight their own stability or architectural advantages. The spike in Blacksky migrations is a direct example of users seeking stability elsewhere within the AT Protocol ecosystem, but some may opt for entirely different platforms.
- Security Posture and Investment: This incident will undoubtedly force Bluesky to re-evaluate and potentially significantly enhance its DDoS mitigation strategies and overall cybersecurity infrastructure. While no system is impenetrable, a "sophisticated" attack implies the need for advanced, multi-layered defenses, which can be costly and complex to implement, especially for a relatively young company. This attack serves as a stark reminder that even decentralized platforms are not immune to centralized points of failure, particularly at their primary PDS.
- Perception of Decentralization: While the AT Protocol’s architecture allowed other instances to remain functional, the primary Bluesky application’s struggles might inadvertently cast a shadow on the perceived robustness of decentralized social networks in general. It highlights the need for continuous development of resilient infrastructure, clear communication, and seamless user migration tools to truly realize the benefits of decentralization during crises.
Industry Context: The Rising Threat of Cyberattacks
Bluesky’s current ordeal is not an isolated incident but rather a symptom of a growing global trend: the increasing frequency, sophistication, and scale of cyberattacks. DDoS attacks, in particular, remain a persistent and evolving threat across all industries. Threat actors are continually developing new methods to bypass defenses, utilizing larger botnets and more complex attack vectors.
Reports from cybersecurity firms consistently show an upward trend in DDoS attack volumes and intensity. For instance, a Cloudflare report noted a significant increase in application-layer DDoS attacks in recent years, often targeting critical web services. The motivations have also broadened, with geopolitical tensions, economic disruption, and even casual "griefing" contributing to the landscape of cyber warfare. For tech companies, especially those in the public-facing social media sphere, robust cybersecurity measures are no longer just a technical requirement but a fundamental business imperative. Companies are investing heavily in advanced threat intelligence, AI-driven anomaly detection, and partnerships with specialized DDoS mitigation services to protect their digital assets and ensure service continuity. Bluesky’s experience underscores the constant vigilance required to operate in this hostile digital environment.

Path Forward and User Trust
As Bluesky continues its battle against the ongoing cyberattack, the immediate priority is to fully mitigate the DDoS onslaught and restore stable, consistent service for all users. The promised update on Friday afternoon is crucial for providing transparency and demonstrating progress to a frustrated user base.
Beyond the immediate crisis, this incident will likely prompt a thorough review of Bluesky’s security architecture and incident response protocols. For a platform built on the promise of a more open, resilient, and user-controlled social internet, proving its ability to withstand such attacks is critical for long-term viability and growth. Rebuilding and reinforcing user trust will be an ongoing effort, requiring not just technical fixes but also consistent, clear communication and a demonstrated commitment to security and uptime. The incident, while challenging, also presents an opportunity for Bluesky to showcase the inherent resilience and flexibility of the AT Protocol by facilitating smoother transitions for users to other instances and reinforcing the advantages of a truly decentralized ecosystem. The future success of Bluesky will heavily depend on how effectively it learns from this experience and strengthens its defenses against the ever-present threats of the digital world.